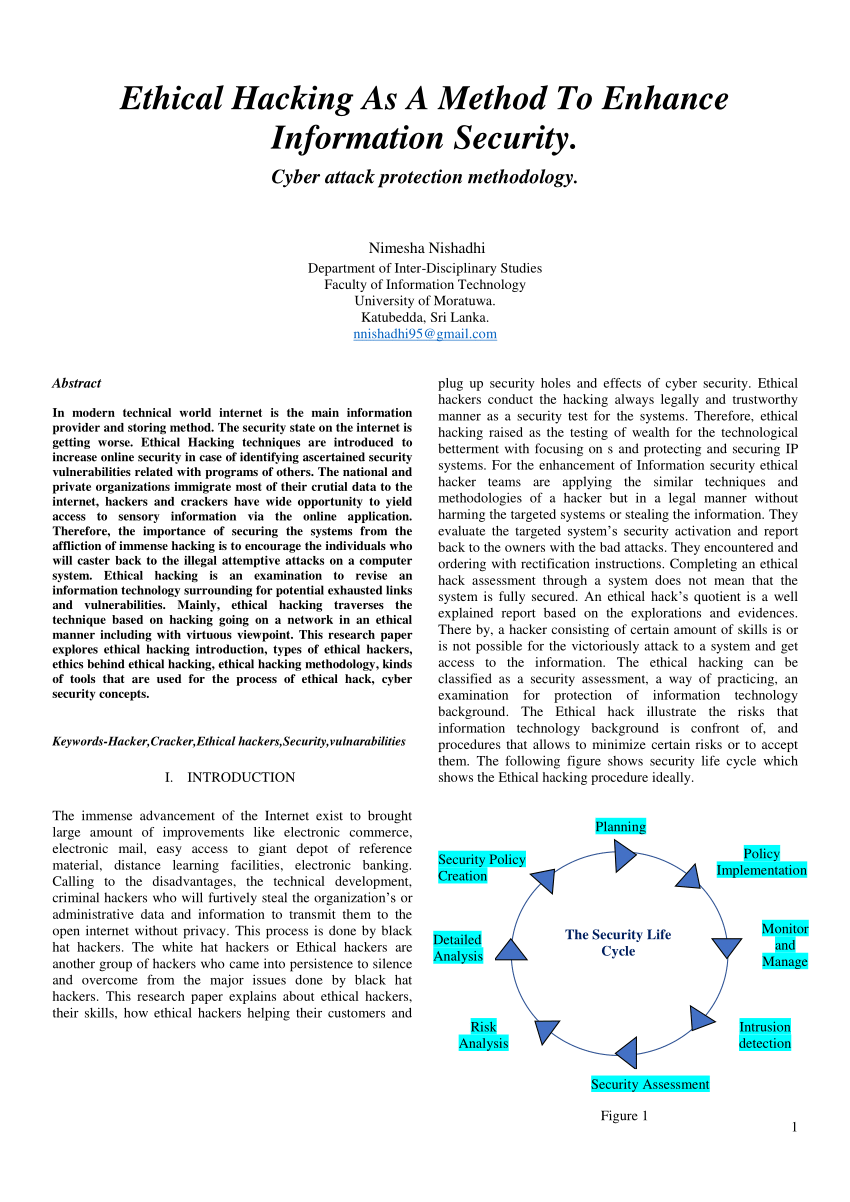
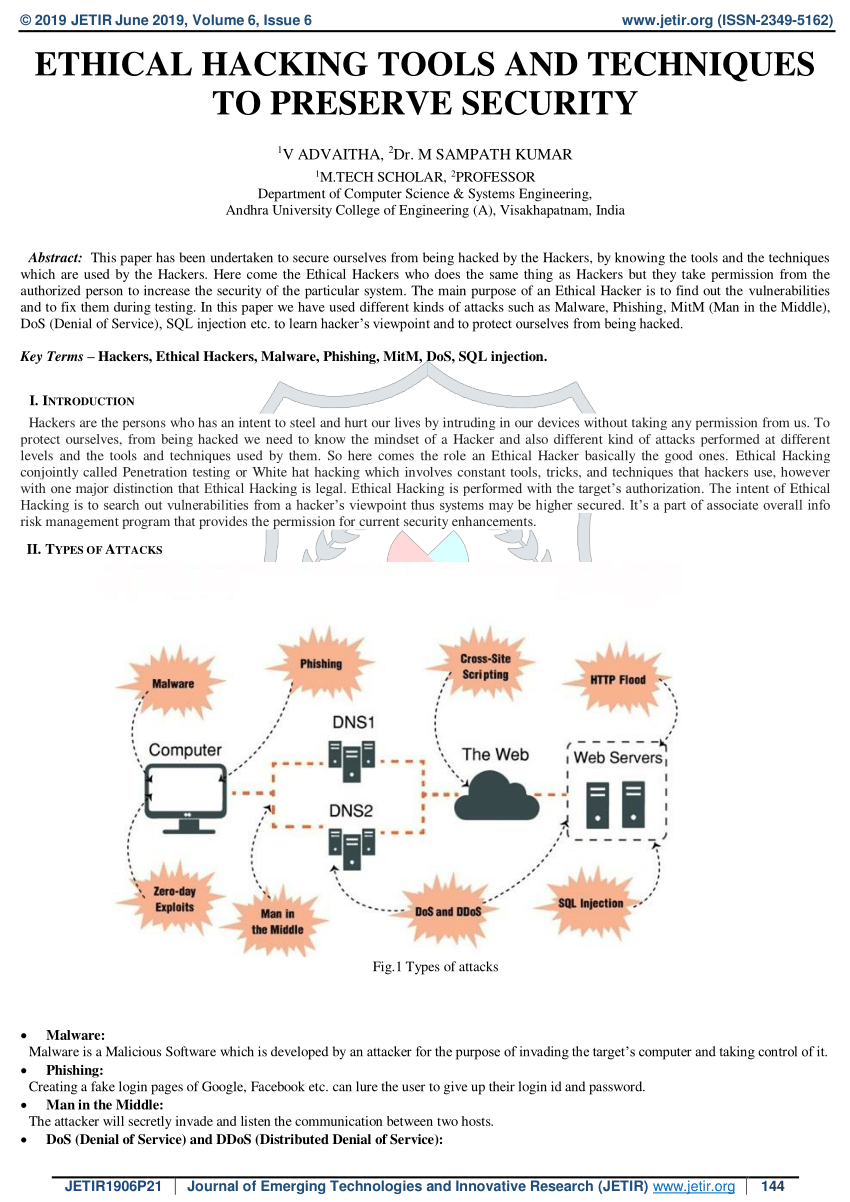
PDF) ETHICAL HACKING (Tools, Techniques and Approaches | steve deluxez and Alok Singh - Academia.edu

PDF) The Importance of Ethical Hacking Tools and Techniques in Software Development Life Cycle | WARSE The World Academy of Research in Science and Engineering - Academia.edu

Beginning Ethical Hacking with Kali Linux: Computational Techniques for Resolving Security Issues ( PDFDrive ).pdf

Reconnaissance for Ethical Hackers: Focus on the starting point of data breaches and explore essential steps for successful pentesting: Singh, Glen D.: 9781837630639: Amazon.com: Books
Stream episode Ethical Hacking Tools And Techniques by Narang Yadav podcast | Listen online for free on SoundCloud














![Ethical Hacking Guide for Beginners [Basics of Ethical Hacking pdf] Ethical Hacking Guide for Beginners [Basics of Ethical Hacking pdf]](https://www.simplilearn.com/ice9/ebooks/CEH_FRS.jpg)